Unfortunately recent MacPorts comes with mod_security 1.8.6 and the maintainer is not actively supporting updates (for details see this ticket). Since I wanted to test some settings on a local Apache installation on my Mac with the latest release (2.5.11) I used the information given in the ticket to patch and update my mod_security port.
This guide is straight forward and shows just the required changes, a working MacPorts installation with Apache 2 is mandatory. You simply have to edit the Portfile that contains the details for mod_security.
Step-by-step explanation
- Update your MacPorts installation by
sudo port selfupdateandsudo port upgrade outdated(read this guide for more details on MacPorts selfupdate) - Open the portfile for mod_security and replace the content of the file with the provided code. The portfile in my installation resides in
/opt/local/var/macports/sources/rsync.macports.org/ release/ports/www/mod_security/Portfile
- Now you may install
mod_securityvia MacPorts using this terminal command:sudo port install mod_security
- Open the Apache configuration file (
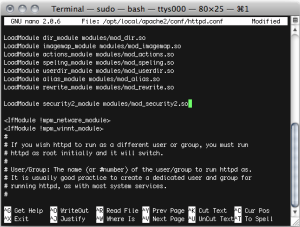
/opt/local/apache2/conf/httpd.conf) in a text editor and addmod_securityto the list.Open a new Terminal (the Termin.app resides in /Applications/Utilities on your harddrive) window and then type the following command to open and edit the file (thesudocommand is required to get write-access to this file since it is normally not writable for you user account).sudo nano /opt/local/apache2/conf/httpd.confNow enter your password (the same you use to log in to your Mac). Use the cursor keys to scroll down to the section for the Dynamic Shared Object (DSO) Support and copy the following line below the last LoadModule… statement (see screenshot).LoadModule security2_module modules/mod_security2.soTo save and leave the Nano editor press CTRL+X and confirm with Y (for Yes) to save.
- Reload the Apache server. The security module should now be loaded by Apache (start or restart Apache to commit changes).
sudo /opt/local/etc/LaunchDaemons/org.macports.apache2/apache2.wrapper restart